Overview
FSO communications have built-in interception resistance due to the way information is sent. Consider first how a radio-frequency signal is sent. RF signals are broadcast over an area and are then funneled with point-to-point connections whereas FSO is exclusively point-to-point. Since RF is broadcast, an eavesdropper of an RF signal doesn’t sap much power from the signal at a legitimate receiver, making it hard to tell if someone is listening. However, since an FSO link is strictly point-to-point, a listener would have to put their device directly in the path of transmission, causing a considerable loss in power and alerting both the legitimate receiver and the legitimate transmitter that someone is listening in.
However, there is the possibility of using reflections off air particles to listen in to FSO signals. For example, an OGS transmits data from the ground to a satellite in the sky using a laser. A few clouds come across the laser and the light is partially reflected and scattered back to the ground. An observer trying to listen in on the communication sees this scattering with certain equipment and is able to “tap” the signal. [1] However, in reality this isn’t likely to occur since the scattered light from the laser would lose too much power before it reaches the ground.
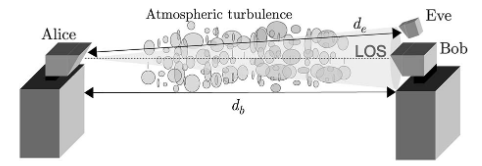
Another variation is to consider a point-to-point link between a laser transmitter and a photodiode receiver (they are connected only by line of sight in free space). A listener could position an interception device in two different places. If the listener is at the receiver end, by angling their receiver toward the transmitter, the listener can observe some divergent light from the source and successfully tap in.
FSO interception at the receiver end by placing the eavesdropping receiver in the divergence profile of the light source
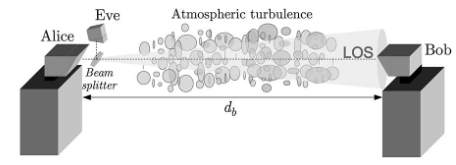
If the listener is at the transmitter end, the listener can deploy a beam splitter to reflect some of the signal up into the eavesdropping receiver while allowing the rest to reach the actual receiver. However, the receiver will notice the loss in power and will likely terminate the link before too much information is lost.
Related Links
Book Section: Link Considerations for FSO Interception Resistance
Paper: Free-Space Optics Communication Platform for Mobile Military Applications